Documentation
Learn how Polypane improves your workflow
Review and approval by IT and Security
This guide gives answers to the most common questions you may be asked by your IT or Security teams in order to get approval for Polypane. For information on procurement, see Sales and Procurement.
If you can't find the answer to a question, reach out to us and we'll do our best to help you.
For enterprise procurement teams requiring a detailed SIG Lite assessment that covers enterprise plans, contact us and we'll provide one on request.
General Info
Description of your product or service
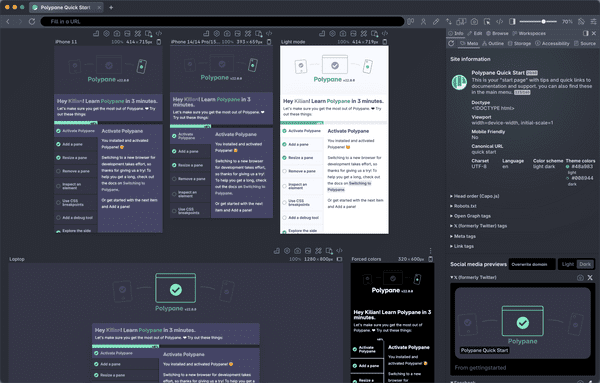
Polypane is a web browser for developers, designers, QA and PMs. It helps you build and test websites that are responsive, accessible and performant.
Type of application
Polypane is a desktop application that can show web pages. It does not edit, manage, transfer or store client or user data. It is comparable to browsers like Chrome, Firefox or Edge — which are likely already running on your organisation's devices — but with extra features for web professionals. Our servers only handle account management and licence verification.
Does Polypane process client data for its customers?
No. Polypane is a desktop application that runs on your computer. It does not store, process or transfer any client data. All data processing happens locally on your machine.
Do you have a designated security/privacy lead who manages your security program? Provide contact information.
Yes. Kilian Valkhof, Founder, kilian@polypane.app
Do you have publicly published privacy and security policies? Provide public links to your Privacy and Security policies.
Do you have a customer information policy?
Data protection role
Controller
Do you have a data access control policy with monitoring? List the roles in the organization who have access to sensitive data.
Polypane is developed by a solo founder that can access sensitive data when resolving customer issues. Sensitive data is limited to very little PII: Name, E-mail address and account status.
Do you have a 3rd party vendor assessment and data access policy? List the roles of any 3rd party to the organization who may have access to sensitive data and under what circumstances.
See our Privacy policy to understand how we interact with third parties. We have DPAs for all parties that process our data.
User access and authentication
What authentication methods do you support?
For the main account holder we support username/password and GitHub OAuth. On the enterprise plan we also support SAML SSO.
Users that have access to the Polypane app have their access managed by the main account holder though our dashboard and do not have logins of their own. Their access to the app is handled credential-less through license keys that get sent to their e-mail address upon being requested from inside the Polypane app.
Do you support SSO and SCIM?
Yes. We support SAML SSO and SCIM on our enterprise plan. SAML SSO is used for the main account holder's login. SCIM can be used to automate user access to Polypane through your identity provider. SSO can be set up during account creation, and SCIM documentation is available upon request.
Internal security programs
Does your organization have a security and privacy program and policies?
Yes.
Do you have a passwords policy?
Yes.
Do you have a system access control policy with monitoring?
Yes.
Do you have a server software update policy? Describe the update and patching mechanisms for operating systems and software to ensure that these are kept up to date.
We do regular updates of the operating systems and packages that we use.
Data retention, backups, and policies
Do you have a customer information possession policy? Describe your policy and the conditions for returning sensitive data and destroying the data once the service is terminated.
See Privacy Policy and Terms of Service.
Can you commit to keeping customer information at a strict minimum amount of time after customer stops use?
We delete all information when a customer requests to delete their information. We do maintain that data inside backups for up to thirty days, at which point it's entirely deleted. We retain a users e-mail for up to six months to prevent abuse.
Do you have a procedure for returning personal data in a format allowing data portability?
We can export customer data to a CSV upon termination of service if requested by a customer.
Do you retain customer information in backups after a customer has deleted (or requested deletion of) the data?
Yes. We keep backups of user data for up to thirty days.
Incident response and reporting
Do you have an incident response policy? How does your organization define a security incident and personal information data breach.
We handle this on a case by case basis.
Describe how customers will be informed of personal data and data security breaches affecting a customer’s data processed by you and your subcontractors and within what timeframe.
They will be informed via email.
Is there a formal company Risk Management program and process that is documented to identify and monitor risks on an ongoing basis?
No.
Are mitigating processes and controls identified for each information security risk discovered?
Yes.
Is there an independent risk, security assessment, or audit performed on your external third parties?
No.
Are network traffic events logged to support historical or incident research?
No for desktop app. An access log is maintained for the management dashboard.
Miscellaneous
Are all authentication, data transmissions, client,server and web sessions that are transmitting confidential data protected using SSL, SSH, or other transmission encrypted protocol?
Yes, with TLS 1.3
Is access to diagnostic or maintenance ports on network and system devices restricted?
Yes.
Is there a process to restore data to a geographically separate secondary facility in a disaster scenario?
Yes, our hosting includes redundancy.
Is data or sensitive credentials (e.g. passwords) transmitted electronically encrypted?
Yes, HTTPS. Password encryption is handled by Amazon AWS Cognito, which do not disclose their encryption algorithms.
Legislation
EU GDPR compliant; see "Your rights" section of our privacy policy.
Certification
Polypane does not currently have any SOC2/ISO27001/HECVAT certifications or audit. Polypane does not interface with your business logic or store any sensitive PII data.
Our service providers are all SOC2 compliant and we have DPAs with the relevant ones.
- Paddle, our payment provider, which keeps all your payment data (we don't have access to that): https://www.paddle.com/legal/soc-2-compliance
- Supabase, our database provider: https://supabase.com/blog/supabase-soc2
- Sentry, our error logging system: https://docs.sentry.io/product/security/soc2/
- PostHog, our telemetry provider: https://posthog.com/docs/privacy/soc2
- AWS, our email provider: https://aws.amazon.com/compliance/soc-faqs/
Have a question about Polypane?
Reach out via (real human) chat, Slack or our contact form:
Contact SupportBuild your next project with Polypane
- Use all features on all plans
- On Mac, Windows and Linux
- 14-day free trial – no credit card needed